What is a phishing simulation test?
Phishing simulations are getting increasingly popular as a training method deployed by organisations in their security awareness training programmes. Let's take an in-depth look at this technique.
What is a phishing simulation test?
Why do companies need phishing simulation tests?
The phishing simulation test is a hands-on practice
On-premises installation or cloud-based software?
6 Essential features of a phishing simulation test
Cautions before implementing phishing simulation test
What is a phishing simulation test?
A phishing simulation test is a method that organisations use to send deceptive emails to their employees in order to gauge their awareness and reactions toward cyber attacks. It allows you to create realistic phishing attacks to send out to your employees and let them experience what fraudulent emails look like in the workplace.
Your employees will be directly involved in learning about the latest phishing spam and the ways to avoid falling victim. They will get direct practical experience as they apply their learning and learn from their failures.
Through these managed attacks, not only do you suffer no security risk, but you can also gain a better sense of how your business is at risk. A phishing simulation test is often a part of security awareness training (SAT) which aims at providing employees with information to understand the dangers of social engineering, detect potential attacks, and take the appropriate actions.
Why do companies need phishing simulation tests?
Experience is often the best teacher, so facing simulated phishing attacks is a wonderful way for your staff to learn. Phishing simulation is highly recommended by various official agencies because it can effectively prevent data breaches, fund loss, and damage to an organisation’s reputation.
A phishing simulation test shows employees different types of mock attacks, teaches them how to recognize the subtle clues, how to report suspicious emails to your IT department and helps to reinforce good employee behaviour. Simulated phishing allows the direct measurement of staff compliance, and when run regularly, can measure progress in user behaviour.
The phishing simulation test is a hands-on practice
The traditional method of lecture-style anti-phishing training, wherein the trainer basically feeds the participants information in a linear fashion, doesn’t seem effective enough in the modern workplace. The learners in this scenario are passive; their role is simply to listen and perhaps take notes, so there is a limitation to engagement.
Phishing simulation tests are hands-on training with an instructional technique that allows participants to learn by doing. The transfer of learning to the workplace is high because the knowledge and materials are the same as what they will be seeing and dealing with on the job. Getting the results can be an eye-opening experience for them which make them pay closer attention to the risks in the future. Their critical thinking and problem-solving skills will also be enhanced as they are expected to be more self-reliant as they work through the activity.
On-premises installation or cloud-based software?
Anti-phishing tools can come in on-premises installation software and cloud-based software.
- In an on-premises installation, you are responsible for everything except the software itself - the servers, network, security, patches to both the software and the OS, and compliance. You will need to pay more up-front investment and allocation of manpower, such as an IT person, to maintain the system in your own data centre.
- In a cloud-based solution, you don’t maintain any of the infrastructures, and the software does not run on your hardware. Users usually access everything they need through a web browser at any time and from any location. The vendor is responsible for the hardware, software, compliance, and security of your data. Thus, it saves time and human resources from thinking about hardware updates and upkeep. All you need is a login name and password to access the platform and to settle a fixed “per user per month” cost.
More businesses nowadays are moving towards the cloud because it’s more cost-effective and flexible. This article by The European Business Review explaining cloud advantages has summarised it all.
6 essential features of a phishing simulation test
Certain factors should be weighed when selecting a phishing simulation provider. Here are some key features that you should consider.
1. Realistic readily-made templates
Some software come with a template library to let you choose from readily-made phishing email themes that reflect the current trends, such as fake package trackings, delivery confirmations, promotions and password reset due to unauthorized login attempts etc. to test employees’ alertness toward real-life phishing attacks.
This example of readily-made landing page templates can largely shorten the time it takes to create a template on your own and thus, increase your productivity.
2. Easy to customise templates
Besides the readily-made templates, well-designed software should allow you to edit layouts by yourself. You should be allowed to edit content to match the kind of phishing attacks your employees are likely to receive in your industry. Choose vendors who provide a user-friendly interface. Some vendors provide you with an easy drag-and-drop layout builder. You can quickly set up, configure and launch a mock attack in less than 10 minutes.
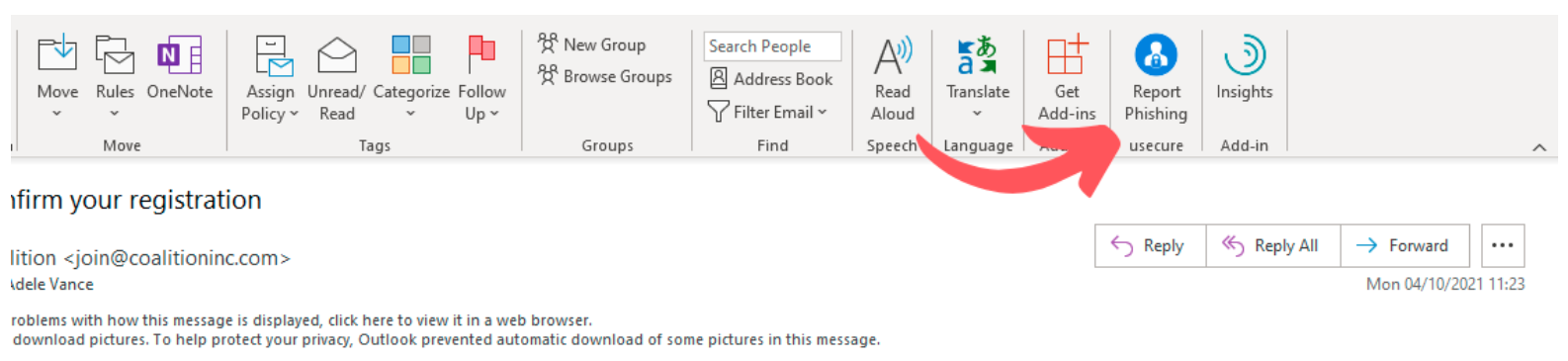
3. A “report phishing” button
You should be allowed to create an easy way that encourages your users to report phishing attempts. This gives you crucial information about what type of phishing attacks are being used. You can also learn what types of emails are getting mistaken for phishing, and what impact this might be having on your organisation.
4. Control and automation
This lets you manage sequencing and specify when and which users will receive tests. You will also be allowed to divide your users into different groups, such as departments or levels, to individualise tests for every employee’s needs. You can also set up automatic regular simulations to test your employees without the manual work needed.
5. Follow-up with compromised employees
Results from phishing simulation should be integrated with phishing tutorial modules and other educating resources to provide closely relevant training to compromised users. In this way, staff who compromised will have the opportunity to recap the key learning points and be more mindful when dealing with future phishing threats. You can also keep tracking and providing them with ongoing training.
6. In-depth reporting
All phishing simulation test results should be recorded into a report for your further analysis Data such as recipient number and identity, participants’ progress, how many attachments were opened or links were clicked through, and how many emails were flagged as suspicious or ignored etc should be listed.
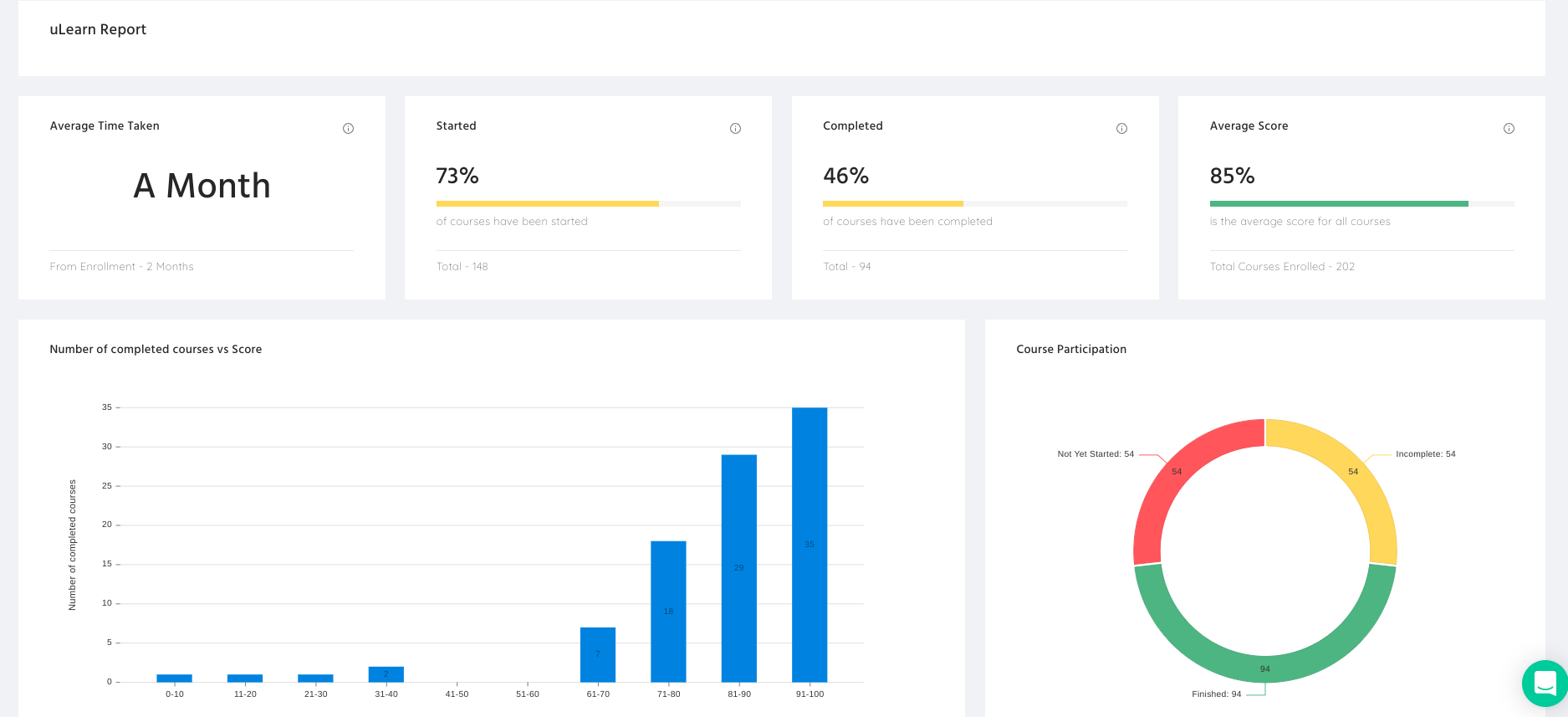
This at-a-glance view makes it easy to see how your users responded to fake emails. You will know which subject lures are the most impactful compared to others and which departments or users are more likely to fall victim etc. It’s a cliché, but data is king within cybersecurity. This data-driven approach gives you measurable advantages and accurate evaluation which helps you to be objective about decisions.
Cautions before implementing phishing simulation test
Obviously, conducting a phishing campaign involves deception. By deliberately sending our employees a link they shouldn’t click on, we raise questions of trust. The followings are important areas that need to be addressed before implementing a phishing simulation test.
-
Employees’ consent
Transparency is a crucial element of phishing testing. Dr John Blythe, head of behavioural science from CybSafe said, “Organizations need to be open with their employees, ensuring they are informing them when they are running a simulated phishing campaign and clearly emphasizing it is designed as an educational tool.” It’s very important that you inform your employees about the tests to explain your rationale and get their consent.
-
Ethical concerns
Certain types of phishing test emails, such as pay rises, promises about bonuses or financial rewards etc should be deployed with caution. West Midlands Trains (WMT) hit the headlines last year due to unethical phishing testing. The company sent emails which appeared to be sent by its finance and payroll department, to about 2,500 employees. The phishing email thanked the staff for their hard work over the pandemic and offered a one-off payment as a reward. However, those who clicked on the link were emailed back with a message telling them it was the company’s “phishing simulation test” and there was to be no bonus.
We are all human and we don’t want to be tricked. As IT managers, we should implement phishing tests for good reasons and in the most acceptable manner. In this way, we can maintain faith in management effectiveness. -
Phishing test performance to be kept confidential
In addition, phishing test performance should be kept confidential once results have been obtained from the testing process. Failing staff shouldn’t be shamed in any way but should be supported by follow-up training. This can truly turn phishing test failures into security wins. After all, employees are a business’s first line of defence, positive encouragement must trump blame-based security culture when it comes to engaging with those who have failed the simulations.
What's the next step?
Proactively measuring employee behaviours is the best way to reduce avoidable security incidents. Train your employees so that they can learn to recognize and report real attacks. By following the guidelines above, you’ve laid the groundwork for what is sure to be a successful phishing test. What’s next? You knew it: Start preparing for your own phishing tests.
How usecure can help?
Don’t let your employees fall victim to phishing attacks. Customise your phishing simulation test today! usecure provides a 100% cloud-based, cost-effective platform for phishing simulation tests. Watch our phishing simulation test demo to learn how to tailor your own phishing simulations to your organization’s needs. We offer a 14-day free trial without credit card information needed. Give it a shot!
.jpg?width=760&name=SAT%20Blog%20CTA%20Images%20(1).jpg)

