The 5 Types Of Employees Phishing Emails Love To Target
All industries are a target for cyber attacks. From financial and manufacturing, right through to health services and charities, nobody is immune.

Few sectors, however, can boast a treasure chest as rich as a legal firms - and criminals know just where to find it.
"The most expensive component of a cyber attack is information loss, which represents 43% of costs."
1# Legal firms
When we say treasure, we mean it. Legal firms have a mountain of client data that cyber criminals are itching to get hold of - and they're fighting off unprecedented attacks to keep this data out of their reach. The struggle is becoming even more tenuous given the widening availability of technology that is making these attacks possible.
Take a look at Ransomware-as-a-Service (RaaS), and you'll find a severely damaging kit of malicious software that's available to anyone - even the less tech-savvy people.
The recent WannaCry ransomware attack that hugely disrupted the NHS (as well as 200,000 other computers in over 150 countries) was the latest big-news breach in the cyber world. Although the old "every cloud has a silver lining" saying might have just proven right with this one, as firms across the UK are deciding to step up their cyber defence strategies.
This is a good step to a much-needed stride for all businesses, although that silver lining might seem rather thin for many law firms, as they are very much viewed as a growing target for current and future cyber attacks.
Next read: 3 of the latest phishing scams you need to avoid in 2019
Like many industries, the digital age means that businesses in the legal sector are storing more and more data online. What separates law firms from many other organisations, is just how valuable the data is that they keep in their grasp. From a client's personal data, right through to intellectual property, cyber criminals are chasing their goal of monetising stolen data, and they know exactly where the treasure is hidden.
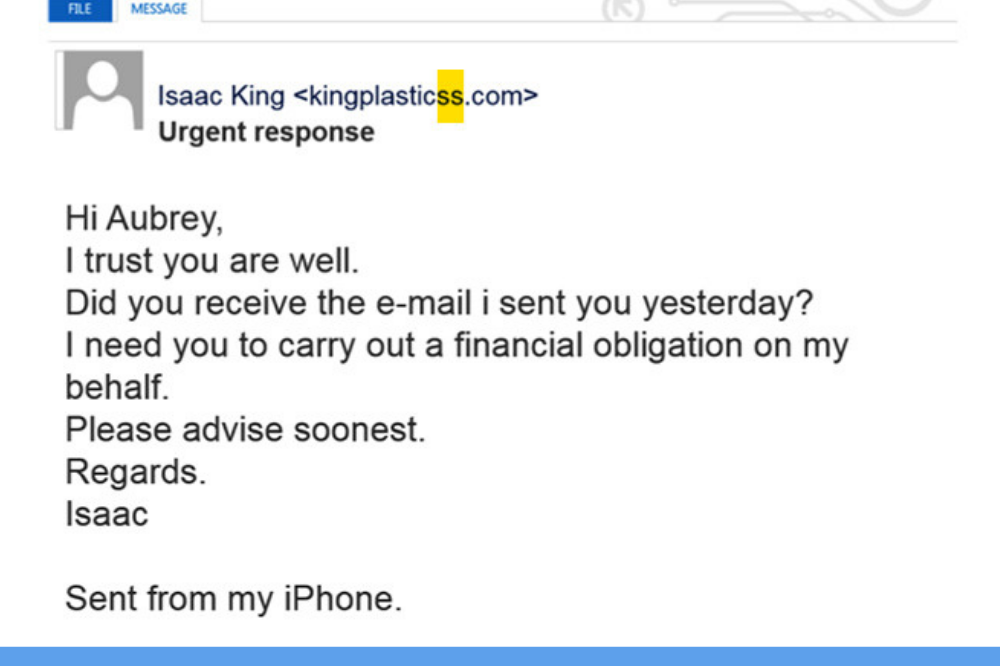
2# Executives/CEOs
CEOs, CFOs and other forms of top executives are some of the most popular phishing targets.
Why?
Because they have access to sensitive information. As well as their authority to sign-off projects and financial transfers. So, what do phishing attacks for executives look like?
These type of attacks are mainly whaling attacks. A whaling attack is a targeted attempt to steal sensitive information from a company such as personal data or financial data. A whaling attack specifically targets senior management, as they will have access to the most valuable data.
As you can see from the example below they're are a few key components that appear in a whaling email:
-
Requesting information or money access
-
A sense of urgency in the email
-
Sent from one person
-
Short and concise email
3# Human Resources
What actually makes HR so attractive to a phisher is simply their access to data. HR teams are responsible for a lot of tasks that involve some form of data such as:
- Recruitment
- On-boarding
- Employee relations
- Payroll.
Many HR professionals have access to financial applications that work in tandem with the payroll departments. These types of records contain very sensitive data that phishers are after. More often than not phishing emails that are sent to HR appear to be from the CEO or a senior level employee. These emails usually request a wire transfer or for the pay roll information to be updated and sent to the phisher.
Here are a few simple steps that your HR staff need to be aware of:
- Be cautious of any "applicants" bringing in CVs on removable media
- Ensure security settings are always in place, especially before uploading any files with confidential information.
- Make sure HR data protection matches the requirements of your country
- The HR team needs to be part of your security awareness training
"Insider attacks account for 70% of cyber attacks"
4# Finance
Every organisation has been exposed to phishing attacks at some point. However, for financial firms, the increase of BYOD means they will encounter more risks.
Why is the financial industry one of the top targets?
One word: Money
The permanence of attacks targeting financial organisations emphasises the fact that more people are using electronic money. This only opens up more opportunities for attackers to strike. Phishers have a wide variety of tactics when attacking a financial company.
Here are a few common examples:
-
Business Email Compromise
-
Whaling
-
Spear phishing
For a more detailed explanation of these types of phishing read this blog: There's plenty more phish in the sea.
5# Legal
The most recent Natwest Legal Benchmarking survey found that 24% of 269 legal firms had experienced a fraud-related loss or cyber attack in the year ending April 2016. Add to that a PwC statistic, cyber attacks on law firms have increased by 60% in the past two years.
"Cyber attacks on law firms have increased by 60% in the past two years"
The legal sector is a vital component fora businesses infrastructure. Law firms are increasingly becoming victims of cyber attacks. With cyber criminals attacking them left right and centre businesses can’t waste any more time, they need to amp up their security awareness.
With these figures in mind, it's clear just how much cyber security needs to be the main priority for any firm. The repercussions of allowing easier access to a cyber criminal can, eventually, tarnish the trust between the lawyer and the client.
Because Law firms have such a variety of sensitive information they become very attractive to cyber criminals. The firms are notoriously known for having low levels of security in place. The information Law firms hold is of such a wide variety and can be anything from employees, payroll and clients. Hackers can use this information to their advantage and could potentially use it for blackmail purposes.
The damage to reputation can be catastrophic to a law firm, not to mention long-lasting. It's time for all legal firms to see data and client information not just as a product, but as one of their crown jewels in need of extra security. Like many industries, the digital age means that businesses in the legal sector are storing more and more data online. What separates law firms from many other organisations, is just how valuable the data is that they keep in their grasp. From a client's personal data, right through to intellectual property, cyber criminals are chasing their goal of monetising stolen data, and they know exactly where the treasure is hidden.
The Threat Of Employees
Whether intentional or not, end users can potentially pose an even bigger risk to security than vulnerable computer systems can. After all, they have legitimate access to a firm's systems and can mistakenly (or intentionally) leak data, and there's a good reason why humans are seen as the weakest point in the security loop. They consume countless information from all kinds of sources, and the rise of human-targeted cyber attacks all provide serious risks.
Being duped into clicking on links that we deem safe from friends and colleagues isn't anything new - but the techniques are changing. This provides an activation point for hackers to exploit weaknesses in a legal firm's computer systems. This along with not being up-to-date on security updates provides the hacker with the ability to take control and cause havoc.
Read more: Your Complete Guide to Phishing
Don't Fall For The Same Old Trap
The attack on the NHS in 2017 exploited vulnerabilities in older versions of Windows operating systems and legacy applications that some hospitals were still using. This type of scenario is not too dissimilar from some law firm mergers, where across a whole firm there might be multiple operating systems or ways of working to support old legacy systems. Procuring long-term investment from the boardroom to upgrade systems remains a challenge.
Risks can be reduced by educating your employees on how to understand how they can protect their business. This is where security awareness programs come in. Giving your employees short and regular modules on the different topics on cyber security with improving their knowledge and confidence when they are faced with an attack. Phishing simulations also work wonders for a business, as they allow the company to phish their own employees and also review what each employee did when they received the email.
When the training and phishing simulations are continuous it allows the end users maintain their knowledge and keep them alert all the time. It puts the employees mind at ease but also the employers.



