Back to Work: How to reduce cyber risks for returning employees
Many people across the globe will be looking to make the transition back into work following the period of lockdown. Here, we outline the main user-focused cyber risks and how to mitigate them.
This is great news for many businesses, but aside from the many health safety challenges, there will also be cyber security challenges faced during this time.
It will be more important than ever for companies to cover the main security training topics when preparing to return to work.
As we have seen, there was an increase in phishing attacks during the Coronavirus outbreak, this included an "85% increase in phishing attacks targeting remote workers over the three-month period." Therefore, it is likely that we will see similar attempts by hackers when employees begin to return to work.
Having a good contingency plan for returning to work, and recognising the challenges presented in this article will help enable a smoother transition back into the real-world working environment.
In this article we discuss the main challenges and solutions you can implement:
Good Device Hygiene
As we have been working from home, it has led to a range of new devices, personal computers and mobile phones being connected to company data and accounts.
Devices being at home by your users may have left logged in to company accounts could pose a risk to data and secure systems.
You should:
-
Ensure you’re users are logged out of all company systems on home devices
-
Advise them to delete any company data they have downloaded on your personal devices
-
Advise them to uninstall any VPN software they have downloaded to use to access company networks on home computers
Phishing
Phishing remains the number one cyber security risk to look out for and with transitional work environments, come opportunities for hackers.
During the Coronavirus epidemic there has been a wave of new phishing emails using fear and curiosity about the virus to get victims to download malicious attachments or give up their personal details.
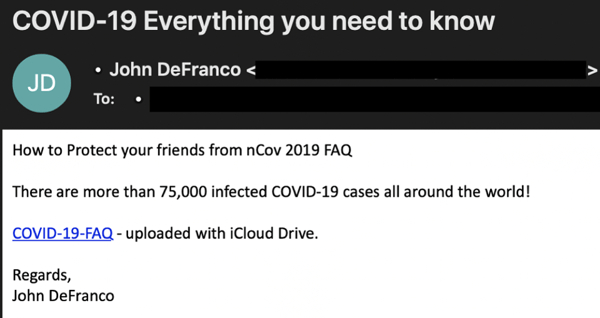
As people are returning to their offices, malicious actors are making use of this opportunity to dupe innocent users.
Employee's should be instructed to:
-
Never send passwords over email
-
Think twice before reacting to an email that tries to create a sense of urgency
-
Never click attachments in unexpected emails before verifying the email with the sender
-
Avoid following links in emails that you didn’t expect to receive
Password hygiene in the office
When returning to the office, employee's will have to log in to devices they may have not been using for a while. They may also have forgotten some of their passwords.
The switch back from personal to work computers or other devices will also pose multiple challenges. We have seen that on personal devices simpler passwords are chosen for simplicity of access.
It’s important to remember that secure passwords are one of the most important keys to protecting devices, systems and data. An insecure password or a password written down for unauthorised users to find can quickly expose the whole company network to infiltration.
Employee's should be instructed to:
-
Ensure all accounts are protected with a strong password or passphrase (Current advice is to pick 3 entirely random words and combine them together to have a strong but memorable password)
-
Never send passwords over email or text, or write them down on paper notes
-
Use account privileges rather than shared passwords with colleagues to access company accounts wherever possible
This may then transfer to the work environment, making password security at work more relaxed, and therefore less secure.
File Transfers
There is also the issue of transferring files from home to work computers. As many people will have been working from personal devices, they may have many documents they need to transfer back to their work computer in order to continue their work.
Our advice here would be to Zip and Encrypt. Then putting these files on an encrypted USB stick or hard drive will make them more secure than simply trying to email to yourself those important or sensitive documents.
Avoid Unauthorised Access
Unauthorised access could lead to devices and physical data such as printed documents becoming stolen or otherwise exposed.
Employee's should be instructed to:
-
Never share or lend their keys or ID card to anyone - even colleagues.
-
Watch out for people following them through locked or swipe-card access doors into secure premises
-
Never leave their keys on desks or in other places where they could be picked up by someone else
Maintain Your Clean Desk Policy
Clean Desk Policies are simple to implement and can be an effective tool against cyber-crime.
Having a work culture which encourages employee's to keep their desk free of clutter ensures that no sensitive documents or devices containing sensitive data are left exposed to an unauthorised person picking them up, even if they were to gain access to the premises.
Employee's should be instructed to:
-
Ensure their desk's are empty at the end of the workday
-
Lock all removable devices and paper documents into secure drawers or cabinets
-
Shred any sensitive paper documents no longer needed
Start preparing to return to work
As we begin to move back to the office environment, it's important to have a good transitional plan in place.
Companies should not rush this and should continue to maintain a secure cyber environment for their employee's.
We have been working to ensure that companies and employee's stay safe and cyber secure during this time. If you would like to see more of our resources, click the link below.


.png)